Use case · regulated workloads
Use cheap storage without trusting the storage provider.
DeltaGlider encrypts objects before they reach the backend. The cryptographic key stays in your trusted environment, while compression can further reduce the storage bill.
live product
Controls
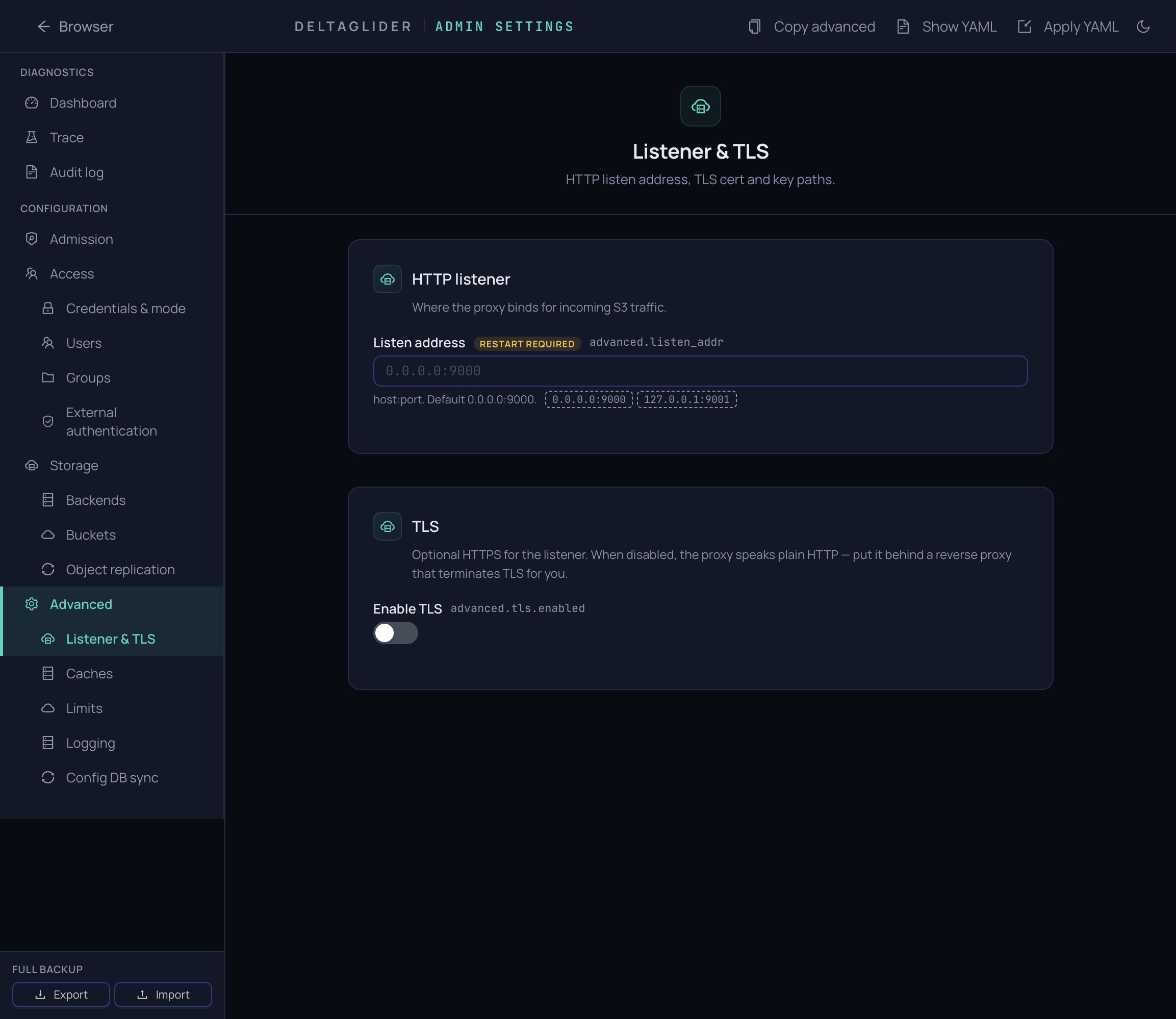
Controls built into the proxy.
The storage provider sees ciphertext. Your runtime keeps the key, policy, and operational controls.
✓AES-256-GCM proxy-side encryption at rest
✓Key supplied from your environment
✓Encrypted SQLCipher IAM/config database
✓ABAC permissions with source-IP and prefix conditions
✓Public read-only prefixes for controlled publishing
✓Soft bucket quotas and bucket freeze
✓Object replication through the engine
✓Audit ring and Prometheus metrics
Real-world scenarios
Common compliance patterns.
The proxy is useful when storage policy needs to stay close to your runtime, not hidden inside one vendor account.
Untrusted low-cost SaaS
A regulated team wants ultra-cheap S3-compatible storage, but cannot trust the provider with plaintext. DeltaGlider encrypts before the backend; the key stays on trusted premises.
Partner downloads
A release bucket needs public read-only access for a few prefixes, while everything else remains private behind IAM.
Secondary copy requirements
A regulated workload needs a cloud copy or offsite prefix. Replication runs through the proxy, so encryption and compression behavior stay consistent.
Evidence
Security features with code behind them.
Proxy-side encryption
Objects are encrypted with AES-256-GCM before they reach the backend. The key is supplied via
src/storage/encrypting.rsDGP_ENCRYPTION_KEY and never leaves your trusted runtime environment.Encrypted config database
Users, groups, policies, and OAuth providers live in SQLCipher. The encrypted DB can sync across proxy instances through S3.
src/config_db_sync.rsABAC access control
Per-user S3 credentials, groups, prefix-scoped resources, and conditions on IP ranges and prefixes using AWS-style policy grammar.
src/iam/permissions.rsObject replication
Copy data through the same control plane.
Replication rules copy objects between buckets or backends while preserving proxy-side encryption and compression behavior.
live product
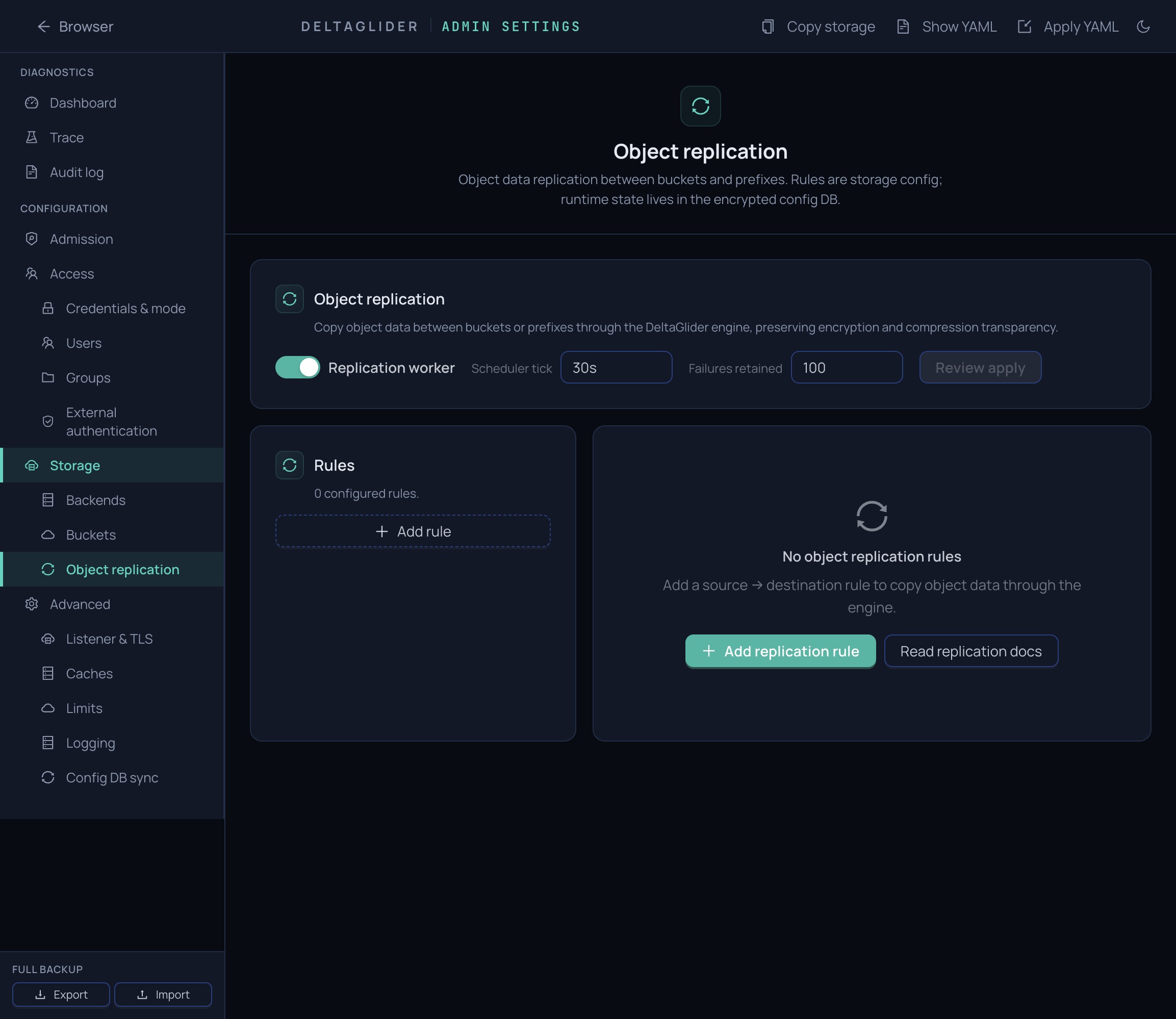
Product view
Pause rules, run now, review history and failures, and replicate deletes when needed.
Next step
Map your storage controls.
Send the requirements that matter: keys, identity, quotas, replication, audit, and deployment constraints.