Use case · MinIO migration
Self-hosted S3 without losing the control plane.
MinIO refugees can find storage engines. What is usually missing is the enterprise control plane: IAM, OAuth, ABAC, bucket policy, quotas, replication, sync, and an operator UI.
live product
The gap
Storage alone is not enough.
The replacement must preserve the operational contract around S3, not only store objects.
✓Per-user S3 access keys
✓Groups with inherited permissions
✓ABAC policies in AWS IAM grammar
✓OAuth/OIDC login and claim mapping
✓Public read-only prefixes
✓Soft per-bucket quotas and bucket freeze
✓Bucket routing aliases
✓Object replication rules
✓Encrypted multi-instance config DB sync
Real-world scenarios
Why MinIO migrations get stuck.
The data path is only one part of the product. The control plane is what keeps production usable.
Storage exists. Control is missing.
You can find younger OSS object stores that move bytes. The hard part is getting IAM, policy, quotas, replication, and operator workflows in one place.
IAM semantics are sticky
Applications already rely on per-user keys, groups, prefixes, and conditional access. Rebuilding that around a storage-only server slows the migration.
Operations need guardrails
Cutovers need soft quotas, bucket freeze, sync state, replication history, and a UI operators can understand under pressure.
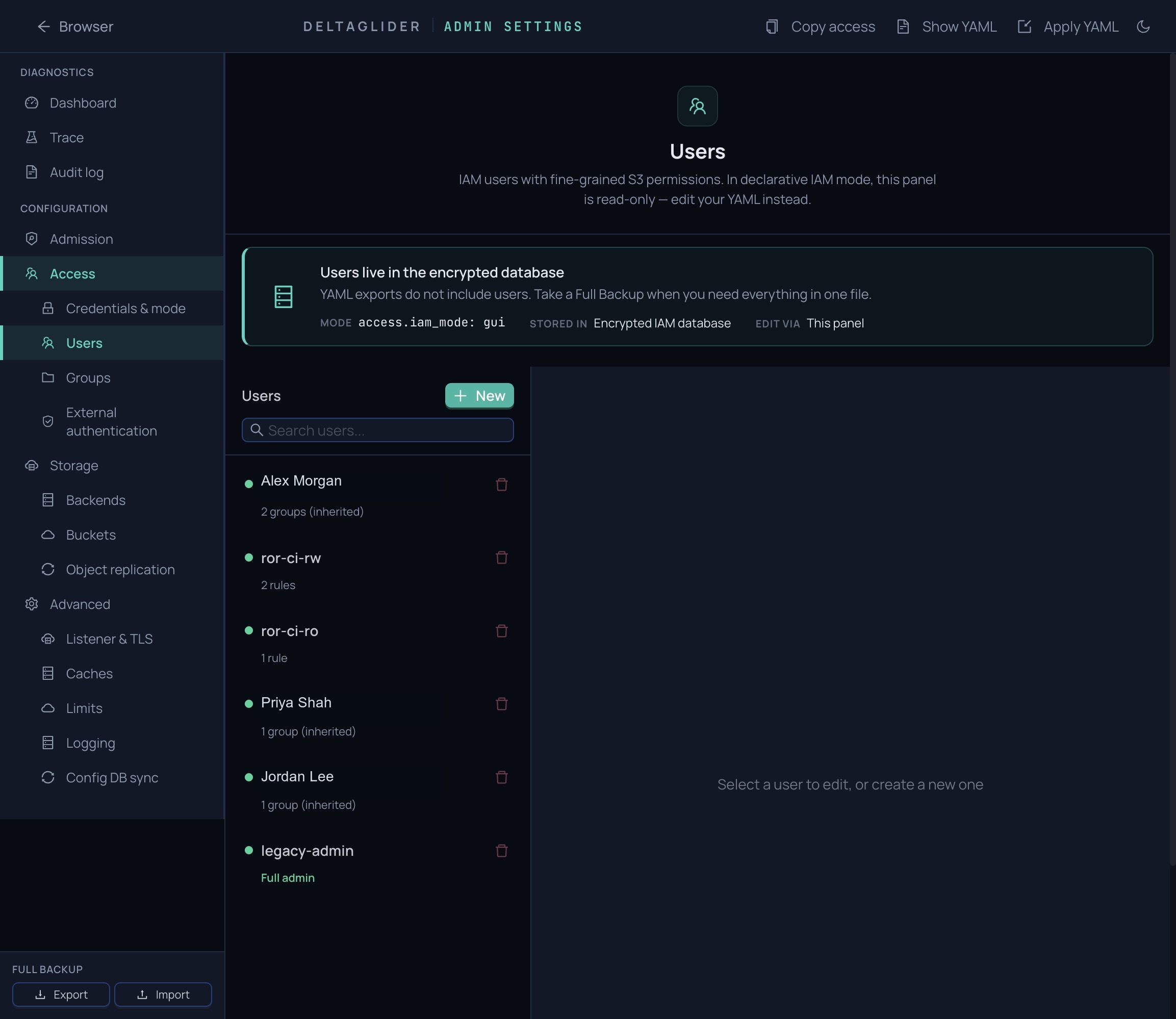
IAM
Enterprise access control for applications and teams.
Per-user credentials
Give applications their own S3 keys. Use groups, inherited permissions, prefix conditions, and source-IP conditions.
src/iam/permissions.rsEncrypted config DB
Users, groups, OAuth providers, and policies live in SQLCipher. Sync the encrypted DB across multiple proxy instances.
src/config_db_sync.rsOAuth and OIDC
Connect a provider and map claims to DeltaGlider groups from the admin UI.
No client rewrite
Keep existing SDKs and tools. The proxy speaks S3 with SigV4, so storage migration does not become an application migration.
Bucket policy
Bucket controls stay in the control plane.
Configure compression, aliases, public prefixes, soft quotas, and read-only freeze per bucket.
live product
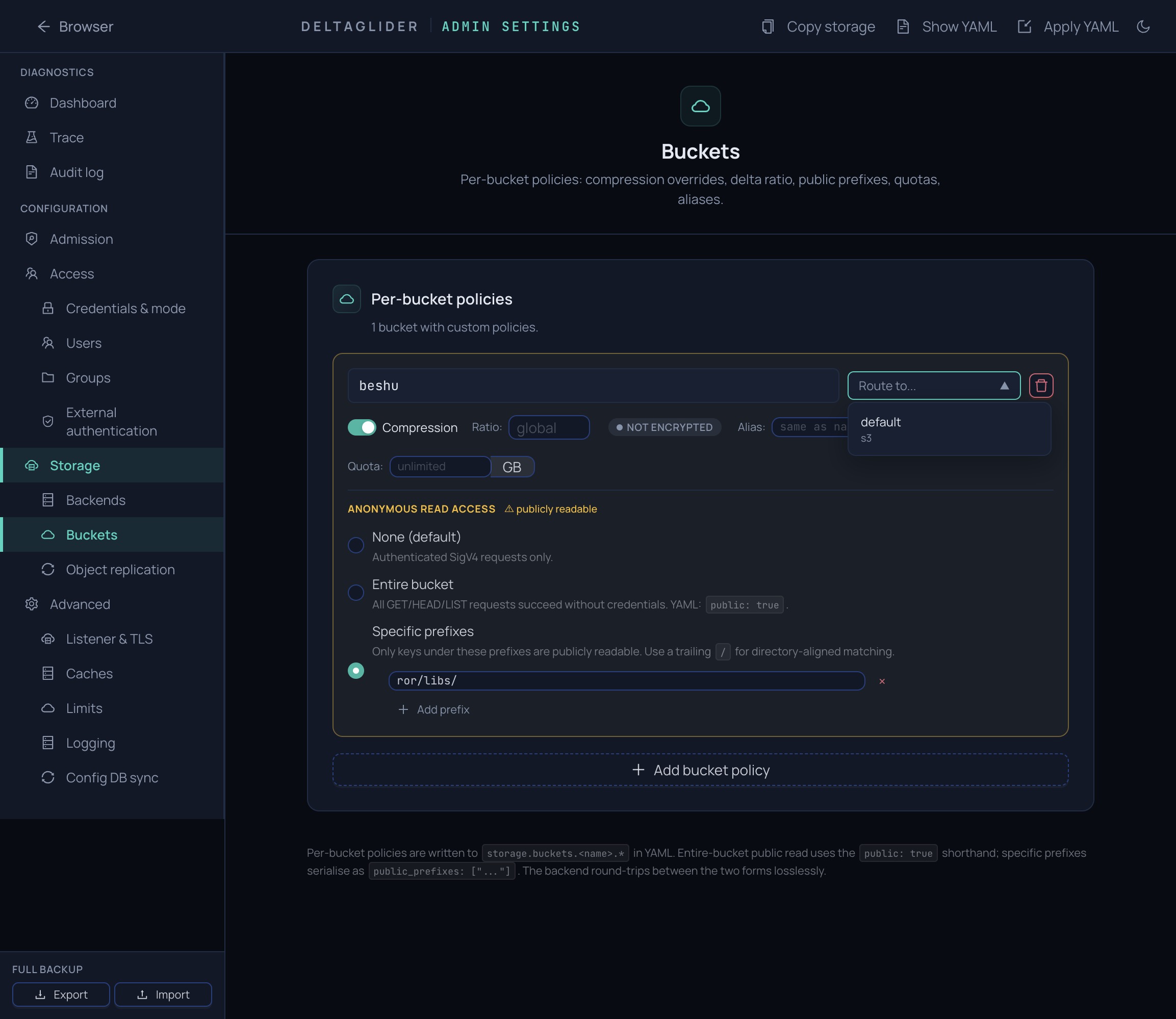
Product view
Bucket policy covers compression, aliases, public prefixes, soft quotas, and frozen buckets.
Quotas
Soft write limits per bucket.
Use soft quotas to control growth. Set quota to zero to freeze a bucket during migration.
Soft cap
Set `quota_bytes` on a bucket. Writes above scanned usage are rejected.
docs/product/10-first-bucket.mdFreeze mode
Set `quota_bytes: 0` to block writes while reads continue.
Operator-visible
Quota is managed next to bucket policy, aliases, and public prefixes.
Next step
Map the control plane before moving bytes.
Share the IAM, bucket policy, quota, replication, and operator workflows you use today. We will map what ports cleanly and what needs adjustment.